● NSE 6 - OT Security 7.6 Architect Exam Materials
Some clients reported that a few new questions appeared on the exam (around 10 new questions).
Please take care of that, and we will update the dump very soon.
Please take care of that, and we will update the dump very soon.
Question #1
Question #2

Refer to the exhibit.
The OT devices behind the ruggedized FortiGate have vulnerabilities and you want to apply a virtual patching profile in the firewall policy.
Why is Virtual Patching not available in the Security Profiles section?
(Choose one answer)
- A. You must enable Virtual Patching in the Feature Visibility section.
- B. You must have a ruggedized FortiGate allowing the virtual patching feature.
- C. You must enable OT signatures.
- D. You must have a valid OT security service license.
Question #3
Which industrial protocol does not support VLANs? (Choose one answer)
- A. not support VLANs? C
- B. Ethernet over industrial protocol
- C. EtherCAT
- D. Modbus over TCP
Question #4
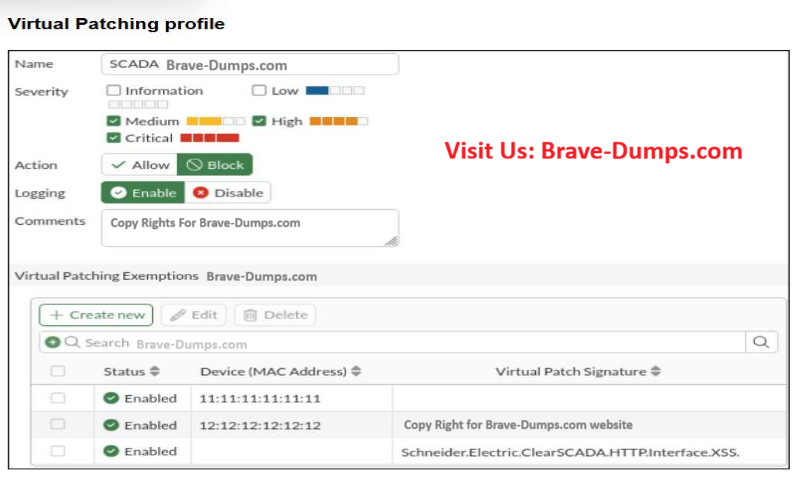
Refer to the exhibit.
A Virtual Patching profile is shown. SCADA
You have recently updated your SCADAsystem and would like to apply the
SCADA virtual patching profile.
Which two statements about this profile are correct?
(Choose two answers)
- A. Only the vulnerability Schneider.Electric.ClearSCADA.HTTP.Interface.XSS is still present.
- B. Low severity signatures are not blocked for the device with the MAC address 12:12:12:12:12.
- C. This profile blocks critical severity signatures for all the devices.
- D. The device with the MAC address 11:11:11:11:11 is considered to have no vulnerabilities.
Question #5
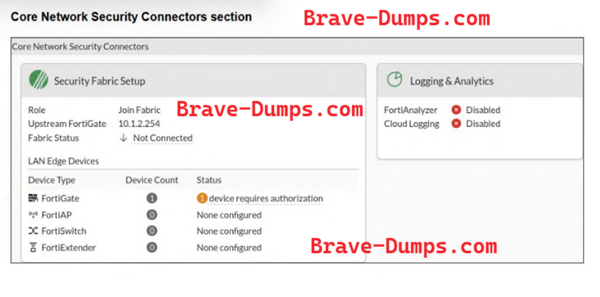
Refer to the exhibit.
The Core Network Security Connectors page of the FortiGate-2 device is shown.
Which statement is correct?
(Choose one answer)
- A. FortiGate-2 serves as Fabric Root.
- B. You must enable Security Fabric Connection on the FortiGate-2 interface.
- C. You must configure the FortiAnalyzer settings on FortiGate-2.
- D. FortiGate-2 is not authorized on the root FortiGate.
Question #6
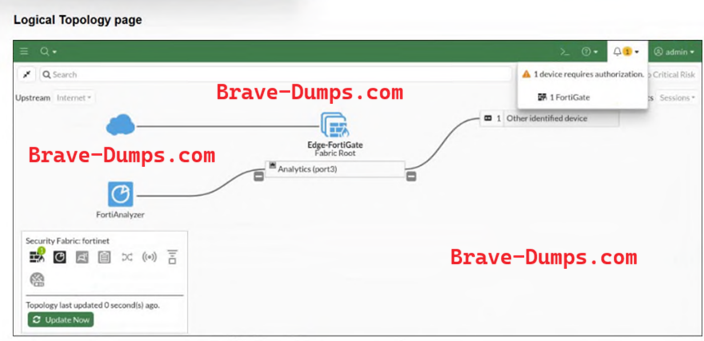
Refer to the exhibit.
A Logical Topology page of a FortiGate device is shown.
Your OT company wants to gain visibility into the network. You decide to
implement device detection with the Security Fabric.
Based on the exhibit, which statement is correct?
(Choose one answer)
- A. Device Detection is enabled on the other identified device.
- B. The other identified device must be authorized on the root FortiGate.
- C. The other identified device must be authorized on FortiAnalyzer.
- D. Device Detection is enabled on port3.
Question #7
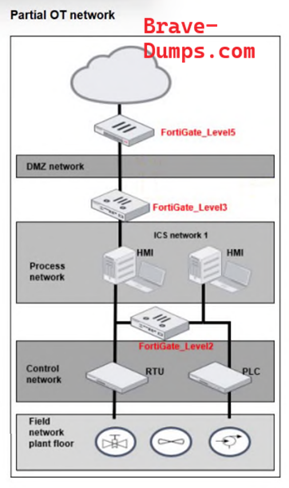
Refer to the exhibit.
A partial OT network is shown.
In this OT network, you must add additional security measures to detect OT protocols and, therefore,
increase the traffic visibility.
Which security sensor must you implement to delect the OT protocols in this network?
(Choose one answer)
- A. Device detection on all the FortiGate interfaces
- B. Inline IDS on FortiGate_Level3
- C. Application sensor set to monitor on all the FortiGate devices
- D. IPS sensor on FortiGate Level5
Question #8
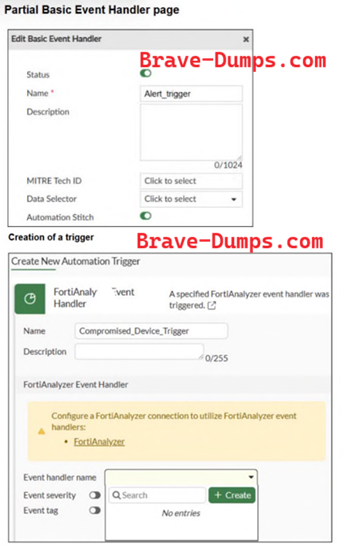
Refer to the exhibits.
A partial Basic Event Handler page on FortiAnalyzer and the creation of a trigger in a FortiGate
device are shown.
To improve the protection of your OT network, you want to automate the handling of compromised
devices notified through FortiAnalyzer.
You have configured an event handler Brave-Dumps.com as shown in the exhibit. When you create the trigger on the
FortiGate device, the Event handler name field does not provide the Alert_trigger option.
What two actions must you perform to make the Alert_trigger option available?
(Choose two answers)
- A. You must click + Create in the Event handler name field.
- B. You must authorize the FortiGate device on FortiAnalyzer
- C. You must configure the FortiAnalyzer setting on the FortiGate device.
- D. You must configure the trigger on the root FortiGate.
Question #9
To improve visibility into the risks in your OT network, you would like to create a new report on FortiAnalyzer.
What must you do to create this report?
(Choose one answer)
- A. Create a template or use an existing one.
- B. Import a report created in FortiSIEM.
- C. Enable the FortiAnalyzer Fabric settings.
- D. Clone a predefined report to create a new one.
Question #10
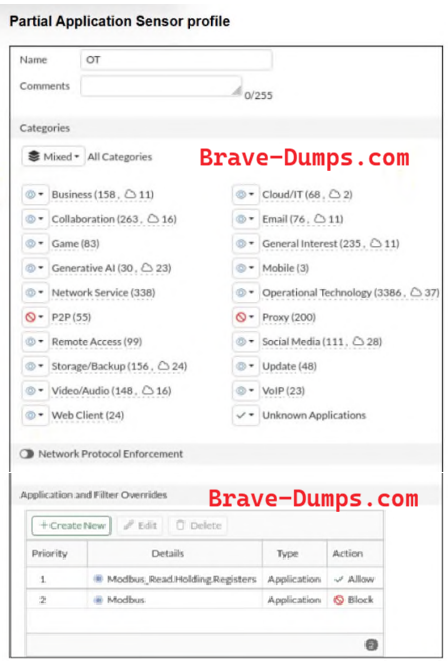
Refer to the exhibit.
A partial Application Sensor profile is shown.
When you apply this profile in a firewall policy, which two statements are correct?
(Choose two answers)
- A. OT signatures are enabled.
- B. All OT protocols are monitored.
- C. Modbus write commands are blocked.
- D. A log is provided for each Modbus read holding registers command.
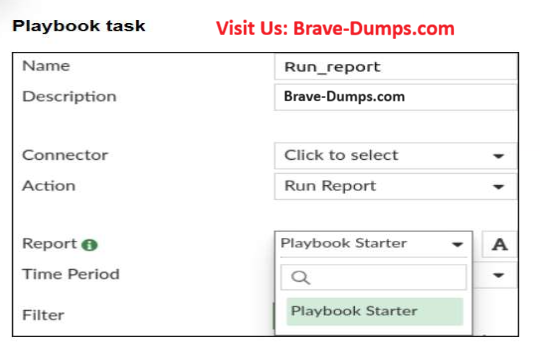
Refer to the exhibit.
A Run_report task is shown.
You want to automate the generation of a newly created report on FortiAnalyzer.
When you configure the Run_report task in Playbook, why is the report not shown in the Report field? (Choose two answers)