● NSE 5 - FortiSASE and SD-WAN 7.6 Core Administrator Exam Materials
Question #1
Question #2
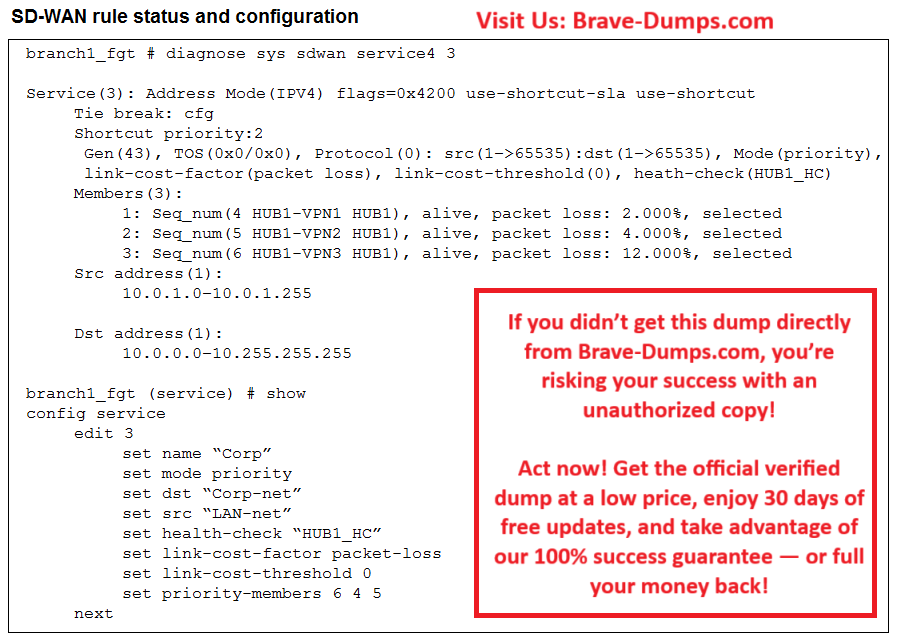
Refer to the exhibit, which shows the SD-WAN rule status and configuration.
Based on the exhibit, which change in the measured packet loss will make HUB1-VPN3 the new preferred member?
(Choose one answer)
- A. When all three members have the same packet loss
- B. When HUB1-VPN1 has 4% packet loss
- C. When HUB1-VPN1 has 12% packet loss
- D. When HUB1-VPN3 has 4% packet loss
Question #3
Which secure internet access (SIA) use case minimizes individual endpoint configuration? (Choose one answer)
- A. Agentless remote user internet access
- B. SIA for FortiClient agent remote users
- C. Site-based remote user internet access
- D. SIA using ZTNA
Question #4
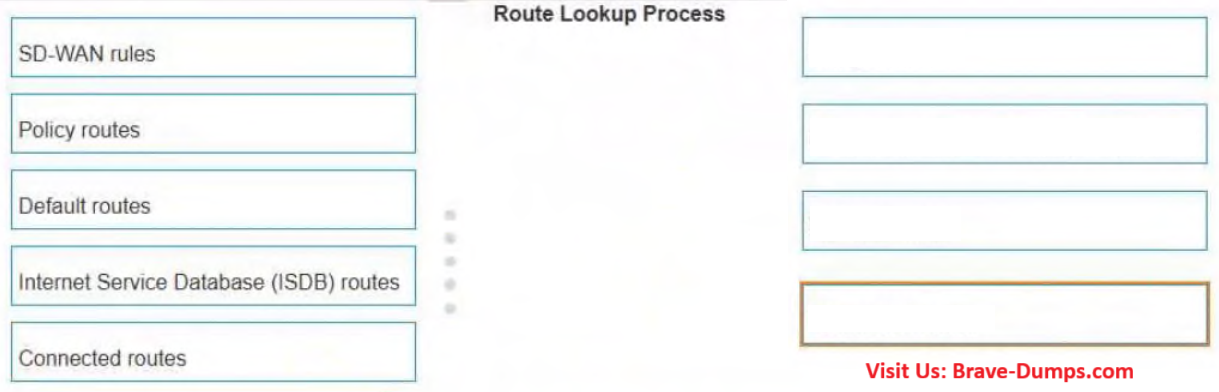
In which order does a FortiGate device consider the following elements shown in the left column during the route lookup process?
Select the element in the left column, hold and drag it to a blank position in the column on the right. Place the four correct elements in order, placing the first element in the first position at the top of the column. Once you place an element, you can move it again if you want to change your answer before moving to the next question. You need to drop four elements in the work area.
Select and drag the screen divider to change the viewable area of the source and work areas.
(Choose four answers)
- A. Route Lookup Process 1: Policy routes
- B. Route Lookup Process 2: Internet Service Database (ISDB) routes
- C. Route Lookup Process 3: SD-WAN rules
- D. Route Lookup Process 4: Default routes
Question #5
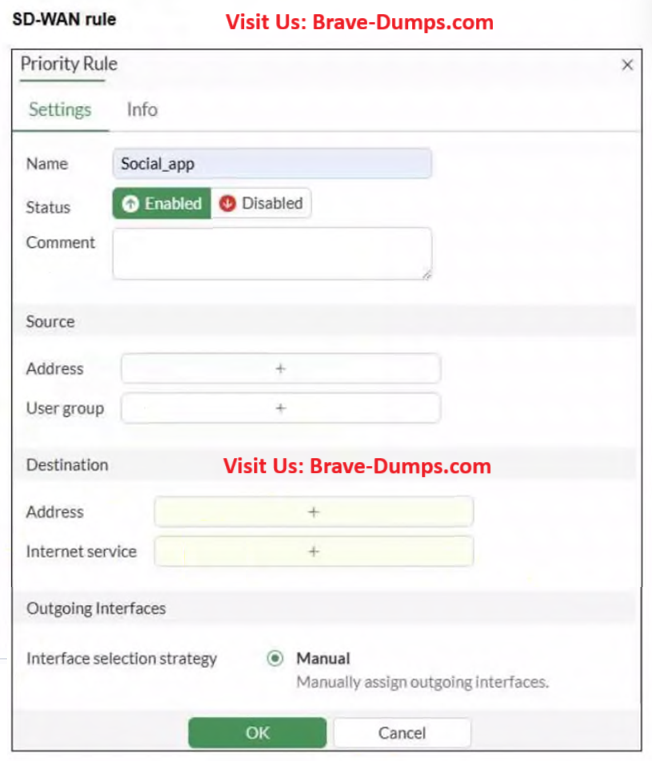
Refer to the exhibit.
You configure SD-WAN on a standalone FortiGate device. You want to create an SD-WAN rule that steers traffic related to Facebook and LinkedIn through the less costly internet link.
What must you do to set Facebook and LinkedIn applications as destinations from the GUI?
(Choose one answer)
- A. Enable the visibility of the applications field as destinations of the SD-WAN rule.
- B. You cannot configure applications as destinations of an SD-WAN rule on a standalone FortiGate device.
- C. Install a license to allow applications as destinations of SD-WAN rules.
- D. In the Internet service field, select Facebook and LinkedIn.
Question #6
Which two statements correctly describe what happens when traffic matches the implicit SD-WAN rule? (Choose two answers)
- A. Traffic is load balanced using the algorithm set for the v4-ecmp-mode setting.
- B. Traffic does not match any of the entries in the policy route table.
- C. FortiGate flags the session with may_dirty and vwl_default.
- D. The traffic is distributed, regardless of weight, through all available static routes.
- E. The session information output displays no SD-WAN service id.
Question #7
How does the FortiSASE security dashboard facilitate vulnerability management for FortiClient endpoints? (Choose one answer)
- A. It automatically patches all vulnerabilities without user intervention and does not categorize vulnerabilities by severity.
- B. It shows vulnerabilities only for applications and requires endpoint users to manually check for affected endpoints.
- C. It displays only critical vulnerabilities, requires manual patching for all endpoints, and does not allow viewing of affected endpoints.
- D. It provides a vulnerability summary, identifies affected endpoints, and supports automatic patching for eligible vulnerabilities.
Question #8
SD-WAN interacts with many other FortiGate features. Some of them are required to allow SD-WAN to steer the traffic.
Which three configuration elements must you configure before FortiGate can steer traffic according to SD-WAN rules?
(Choose three answers)
- A. Traffic shaping
- B. Routing
- C. Security profiles
- D. Interfaces
- E. Firewall policies
Question #9
What is a key use case for FortiSASE Secure Internet Access (SIA) in an agentless deployment? (Choose one answer)
- A. It provides secure web browsing by isolating browser sessions and enforcing data loss prevention for temporary employees.
- B. It acts as a secure web gateway (SWG) distributing a PAC file for explicit web proxy use, securing HTTP and HTTPS traffic with a full security stack, and is ideal for unmanaged endpoints like contractors.
- C. It distributes a PAC file to secure non-web traffic protocols and applies antivirus protection only for managed endpoints.
- D. It requires FortiClient endpoints and supports ZTNA tags to secure all network traffic for unmanaged endpoints.
Question #10
An SD-WAN member is no longer used to steer SD-WAN traffic. You want to update the SD-WAN configuration and delete the unused member.
Which action should you take first?
(Choose one answer)
- A. Move the SD-WAN member to the virtual-wan-link zone.
- B. Disable the interface.
- C. Remove the member from the performance service-level agreement (SLA) definitions.
- D. Delete static route definitions for that interface.
A FortiGate device is in production. To optimize WAN link use and improve redundancy, you enable and configure SD-WAN.
What must you do as part of this configuration update process? (Choose one answer)