● NSE 7 - Security Operations 7.6 Architect Materials
Some clients reported that a few new questions appeared on the exam (around 10 new questions).
Please take care of that, and we will update the dump very soon.
Please take care of that, and we will update the dump very soon.
Question #1
Question #2
Which three are threat hunting activities? (Choose three answers)
- A. Enrich records with threat intelligence.
- B. Automate workflows.
- C. Generate a hypothesis.
- D. Perform packet analysis.
- E. Tune correlation rules.
Question #3
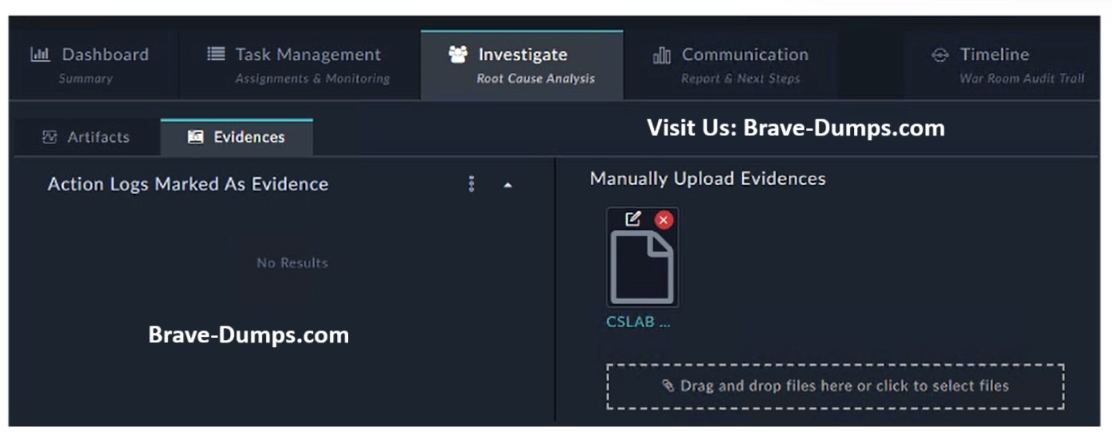
Refer to the exhibit.
How do you add a piece of evidence to the Action Logs Marked As Evidence area?
(Choose one answer)
- A. By tagging output or a workspace comment with the keyword Evidence
- B. By linking an indicator to the war room
- C. By creating an evidence collection task and attaching a file
- D. By executing a playbook with the Save Execution Logs option enabled
Question #4
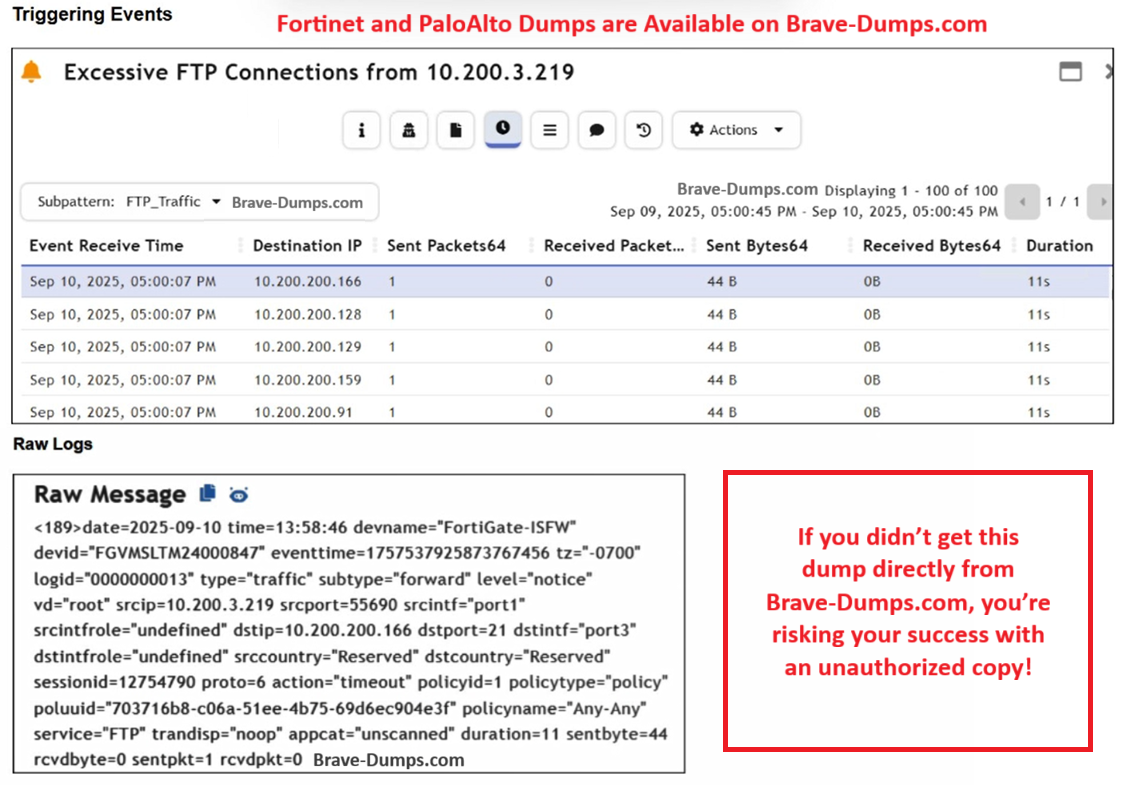
Refer to the exhibits.
Assume that the traffic flows are identical, except for the destination IP address. There is only one FortiGate in network address translation (NAT) mode in this environment.
Based on the exhibits, which two conclusions can you make about this FortiSIEM incident?
(Choose two answers)
- A. The client 10.200.3.219 is conducting active reconnaissance.
- B. FortiGate is not routing the packets to the destination hosts.
- C. The destination hosts are not responding.
- D. FortiGate is blocking the return flows.
Question #5
When you use a manual trigger to save user input as a variable, what is the correct Jinja expression to reference the variable? (Choose one answer)
- A. {{ vars.input.params.<variable_name> }}
- B. {{ globalVars.<variable_name> }}
- C. {{ vars.item.<variable_name> }}
- D. {{ vars.steps.<variable_name> }}
Question #6
Based on the Pyramid of Pain model, which two statements accurately describe the value of an indicator and how difficult it is for an adversary to change? (Choose two answers)
- A. IP addresses are easy because adversaries can spoof them or move them to new resources.
- B. Tactics, techniques, and procedures are hard because adversaries must adapt their methods.
- C. Artifacts are easy because adversaries can alter file paths or registry keys.
- D. Tools are easy because often, multiple alternatives exist.
Question #7
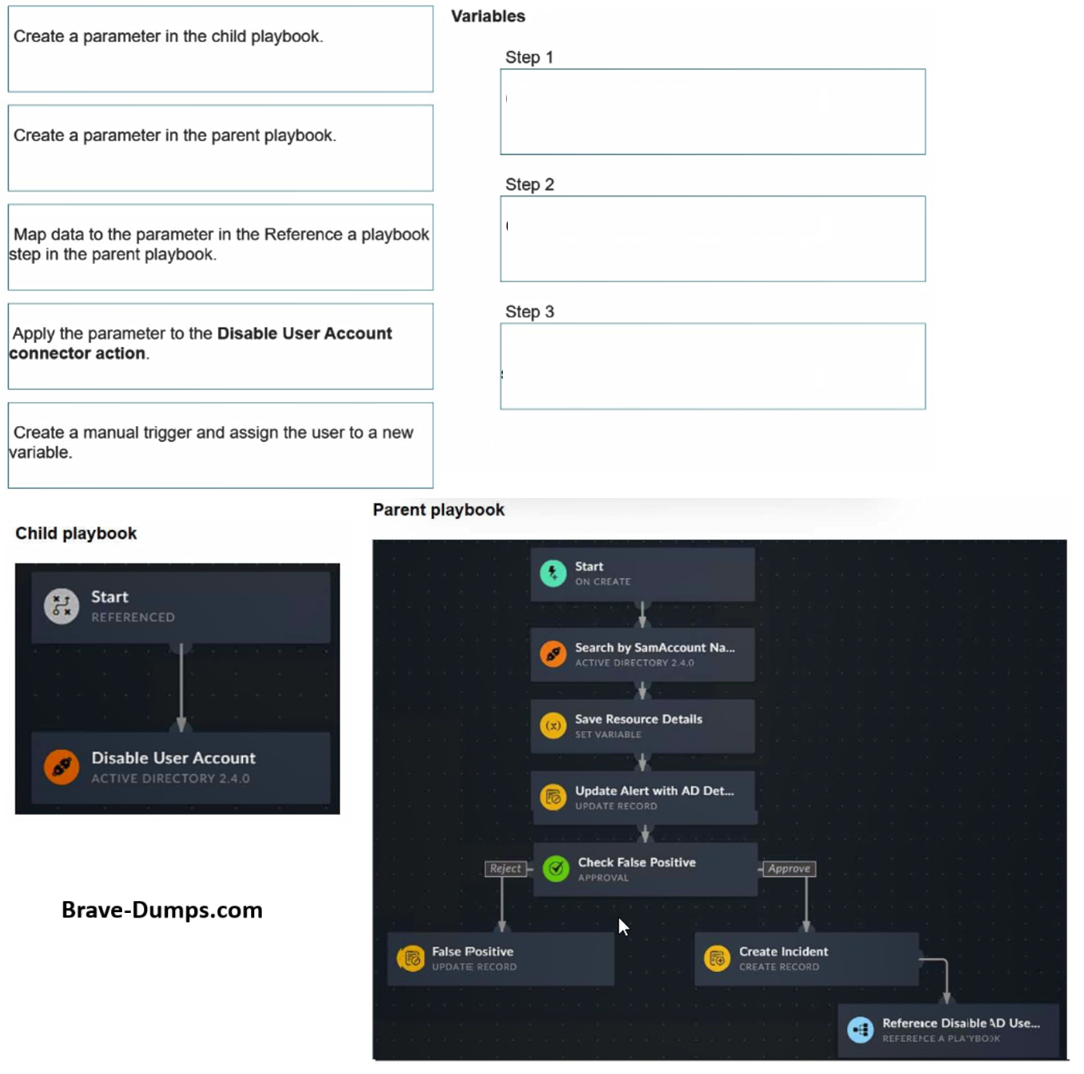
Refer to the exhibits.
You have a playbook that, depending on whether an analyst deems the alert to be a true positive, could reference a child playbook. You need to pass variables from the parent playbook to the child playbook.
Place the steps needed to accomplish this in the correct order:
(Choose three answers)
- A. Step 1 > Create a parameter in the child playbook.
- B. Step 2 > Create a parameter in the parent playbook.
- C. Step 3 > Map data to the parameter in the Reference a playbook step in the parent playbook.
- D. No option D
Question #8
Which three factors does the FortiSIEM rules engine use to determine the count when it evaluates the aggregate condition COUNT (Matched Events) on a specific subpattern? (Choose three answers)
- A. Group By attributes
- B. Data source
- C. Time window
- D. Search filter
- E. Incident action
Question #9
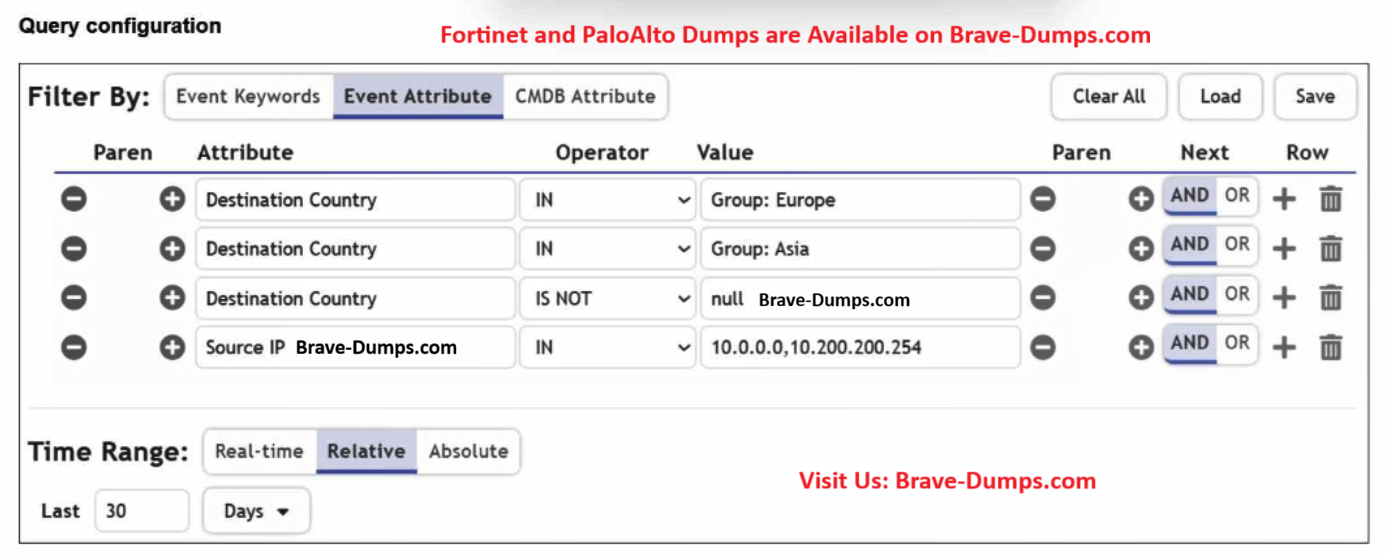
Refer to the exhibit.
You are trying to find traffic flows to destinations that are in Europe or Asia, for hosts in the local LAN segment. However, the query returns no results. Assume these logs exist on FortiSIEM.
Which three mistakes can you see in the query shown in the exhibit?
(Choose three answers)
- A. The null value cannot be used with the IS NOT operator.
- B. The time range must be Absolute for queries that use configuration management database (CMDB) groups.
- C. There are missing parentheses between the first row (Group: Europe) and the second row (Group: Asia).
- D. The Source IP row operator must be BETWEEN 10.0.0.0, 10.200.200.254.
- E. The logical operator for the first row (Group: Europe) must be OR.
Question #10

Refer to the exhibit.
Which method most effectively reduces the attack surface of this organization?
(Choose one answer)
- A. Forward all firewall logs to the security information and event management (SIEM) system.
- B. Enable deep inspection on firewall policies.
- C. Implement macrosegmentation.
- D. Remove unused devices.
Review the incident report
An attacker identified employee names, roles, and email patterns from public press releases, which were then used to craft tailored emails.
The emails were directed to recipients to review an attached agenda using a link hosted off the corporate domain.
Which two MITRE ATT&CK tactics best fit this report? (Choose two answers)