● NSE 6 – LAN Edge 7.6 Architect Exam Materials
● Over 30 Students Passed LAN Edge 7.6 Architect (FCSS_LED-AR-7.6) Using This Dump – Join Them Today!
● Less Than 100 Verified Questions for the NSE 6 – LAN Edge 7.6 Architect Dump (FCSS_LED-AR-7.6 Dump)
● 100% score in the Real LAN Edge 7.6 Architect Exam (LED-AR-7.6 Exam) at the Pearson VUE Testing Center
● Less Than 100 Verified Questions for the NSE 6 – LAN Edge 7.6 Architect Dump (FCSS_LED-AR-7.6 Dump)
● 100% score in the Real LAN Edge 7.6 Architect Exam (LED-AR-7.6 Exam) at the Pearson VUE Testing Center
Question #1
Question #2
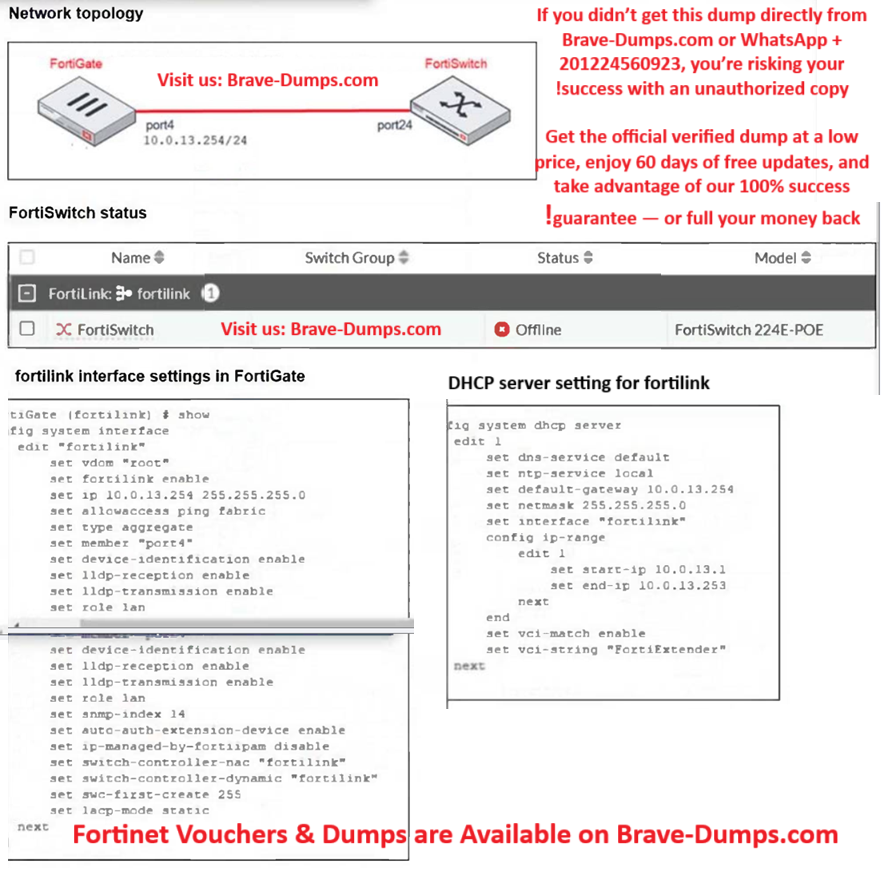
Refer to the exhibits.
You are adding a new FortiSwitch to FortiGate for management. All necessary settings have been configured on FortiGate, but FortiSwitch remains offline. The cabling has been verified and is correctly connected.
Which misconfiguration might be preventing FortiGate from detecting FortiSwitch?
(Choose one answer)
- A. The DHCP server setting vci-string is misconfigured.
- B. The Fortilink interface has the wrong interface member.
- C. The Fortilink interface setting ip-managed-by-fortiipam must be enabled.
- D. The Fortilink interface setting type must be physical.
Question #3
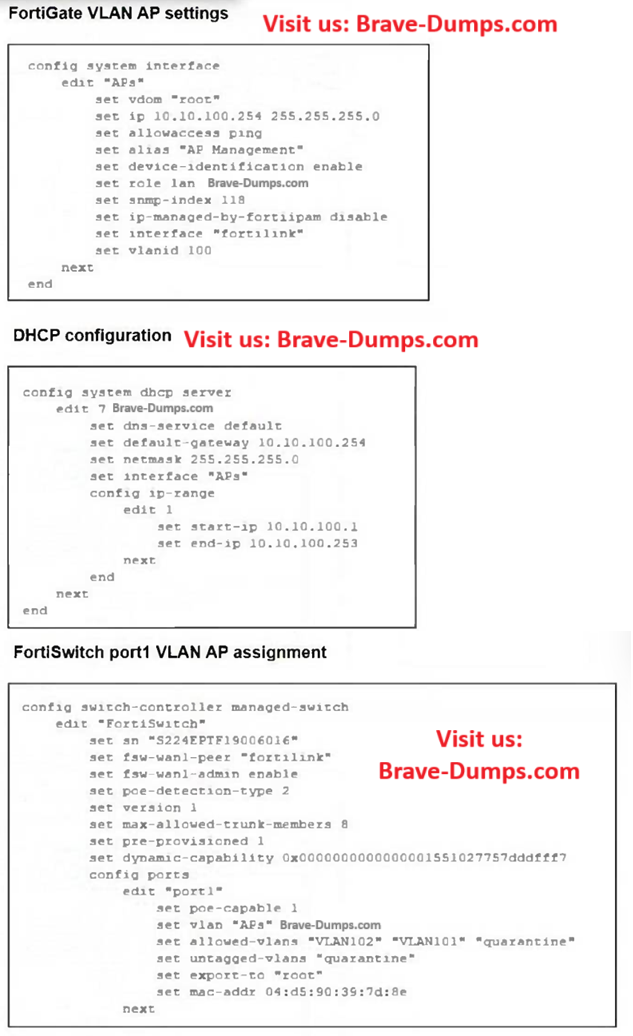
Refer to the exhibits.
A FortiSwitch is successfully managed by a FortiGate. FortiAP is connected to port1 of the managed FortiSwitch.
On FortiGate, the VLAN AP is configured to detect and manage FortiAP, along with a DHCP server for the VLAN AP. Additionally, the VLAN AP is assigned to port1 of FortiSwitch.
However, FortiGate is unable to detect or manage FortiAP.
Which FortiGate misconfiguration is preventing the detection of FortiAP?
(Choose one answer)
- A. The VLAN is not tagged correctly on the FortiSwitch uplink port.
- B. The FortiAP firmware is incompatible with the FortiGate firmware version.
- C. The CAPWAP ports (UDP 5246 and 5247) are not open on FortiGate.
- D. Security Fabric is disabled in the administrative access options of the VLAN.
Question #4
You need to optimize your wireless network to improve performance and reliability in a dynamic environment. The network must adapt to changes in the radio frequency (RF) environment, such as interference, new devices, and fluctuating traffic patterns.
Which role does FortiAIOps play in monitoring and automatically adjusting to changes in the radio frequency (RF) environment?
(Choose one answer)
- A. To detect and report interference and congestion, helping to optimize wireless performance and coverage
- B. To limit the number of devices connected to each access point in a given area
- C. To increase the signal strength of the network if required by modulating power levels on all access points
- D. To monitor network traffic and recommend firewall rules in real time
Question #5
You have decided to manage multiple FortiSwitch devices using FortiManager and its FortiSwitch Manager feature.
Which two statements accurately describe FortiSwitch Manager feature functionality?
(Choose two answers)
- A. FortiSwitch Manager displays the following statuses for FortiSwitch: online, offline, unauthorized, and unknown.
- B. Per-device management is useful for deploying multiple switches with the same configuration.
- C. FortiSwitch Manager displays the following statuses for FortiSwitch: active, inactive, pending, and unknown.
- D. In per-device management mode, you apply settings and profiles to individual FortiSwitch devices.
Question #6
In a public key infrastructure (PKI), what is the primary role of a certificate revocation list (CRL)? (Choose one answer)
- A. To enable certificate authorities to update certificates with new public key information.
- B. To list expired certificates and ensure they are not used for encryption.
- C. To provide information about the revocation status of certificates in real time.
- D. To maintain a list of certificates that have been revoked by the certificate authority (CA) before their expiration date.
Question #7
A conference center wireless network provides guest access through a captive portal, allowing unregistered users to self-register and connect to the network.
The IT team has been tasked with updating the existing configuration to enforce captive portal authentication over a secure HTTPS connection.
Which two steps should the administrator take to implement this change?
(Choose two answers)
- A. Enable HTTP redirect in the user authentication settings.
- B. Update the captive portal URL to use HTTPS on FortiGate and FortiAuthenticator.
- C. Create a new SSID with the HTTPS captive portal URL.
- D. Disable HTTP administrative access on the guest SSID to enforce HTTPS connection.
Question #8
Which two broad categories must be considered for wireless troubleshooting when evaluating key wireless metrics? (Choose one answer)
- A. Wireless range and network speed
- B. Signal interference and device compatibility
- C. Network reliability and signal interference
- D. Wireless health and wireless capacity
Question #9
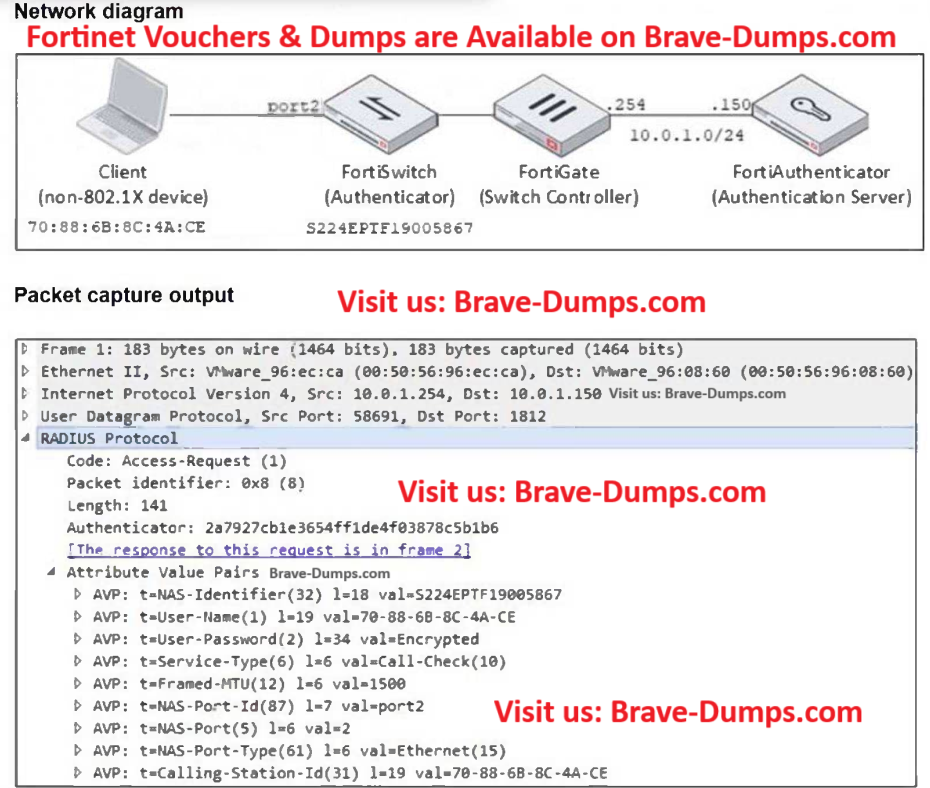
Refer to the exhibits.
Examine the network diagram and packet capture shown in the exhibit.
During packet capture analysis, a RADIUS Access-Request packet was detected being sent from FortiSwitch to FortiAuthenticator and passing through FortiGate. The capture shows that the User-Name attribute in the RADIUS Access-Request packet contains the client MAC address.
Why is the client MAC address contained in the User-Name attribute of the RADIUS Access-Request packet?
(Choose one answer)
- A. FortiAuthenticator is authenticating the client based on the device hostname.
- B. FortiAuthenticator is performing machine authentication.
- C. MAC address-based authentication is being used for the client through MAC Authentication Bypass (MAB).
- D. FortiGate is authenticating the client using 802.1X authentication.
Question #10
How does the Syslog-based single sign-on (SSO) feature in FortiAuthenticator function to correlate user activity with authentication events across multiple network devices? (Choose one answer)
- A. It uses syslog messages to monitor authentication events and correlate them with user activities.
- B. It modifies user credentials based on the outcome of authentication events.
- C. It relies on external servers to analyze syslog messages for user authentication.
- D. It authenticates users through a captive portal by monitoring login attempts.
What is the primary benefit of the LAN Edge solution? (Choose one answer)