● NSE 8 - Written (NSE8_812) Exam Materials
Please note that the exam "NSE 8 - Written (NSE8_812)" is no longer offered by Fortinet and is not available for booking through Pearson VUE, so we opened it on free view,
Question #1
Question #2
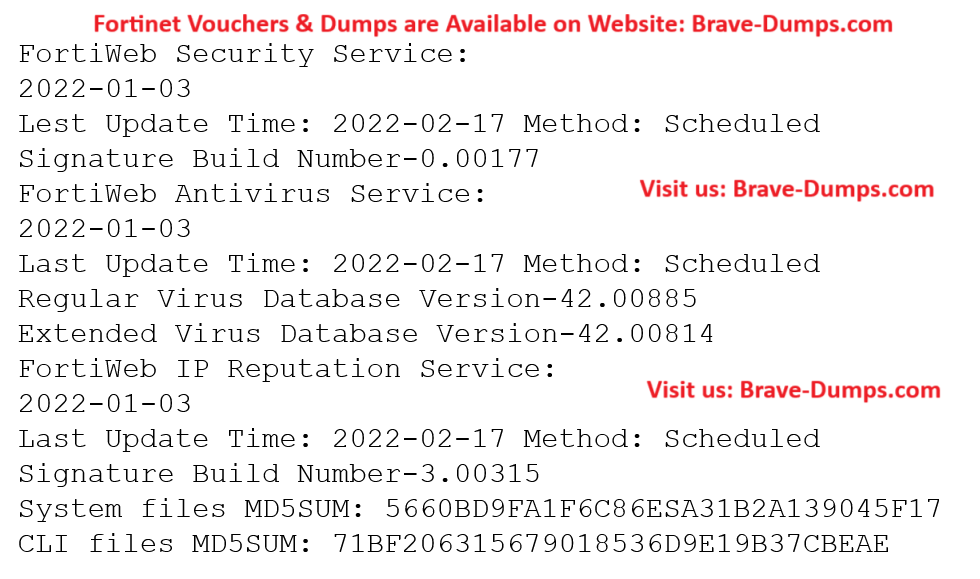
Refer to the CLI output:
Given the information shown in the output, which two statements are correct?
(Choose two answers)
- A. Geographical IP policies are enabled and evaluated after local techniques.
- B. An IP address that was previously used by an attacker will always be blocked.
- C. The IP Reputation feature has been manually updated.
- D. Reputation from blacklisted IP addresses from DHCP or PPPoE pools can be restored.
- E. Attackers can be blocked before they target the servers behind the FortiWeb.
Question #3
Refer to the configuration snippet:
config ips global
set np-accel-mode basic
set cp-accel-mode none
end
What will happen if you change the basic parameter in set cp-accel-mode to advanced?
(Choose two answers)
- A. The CP ASIC will start processing all IPS traffic.
- B. nTurbo will be enabled.
- C. The flow-based IPS signature correlation will be offloaded.
- D. Enhanced IPSA will be enabled.
Question #4
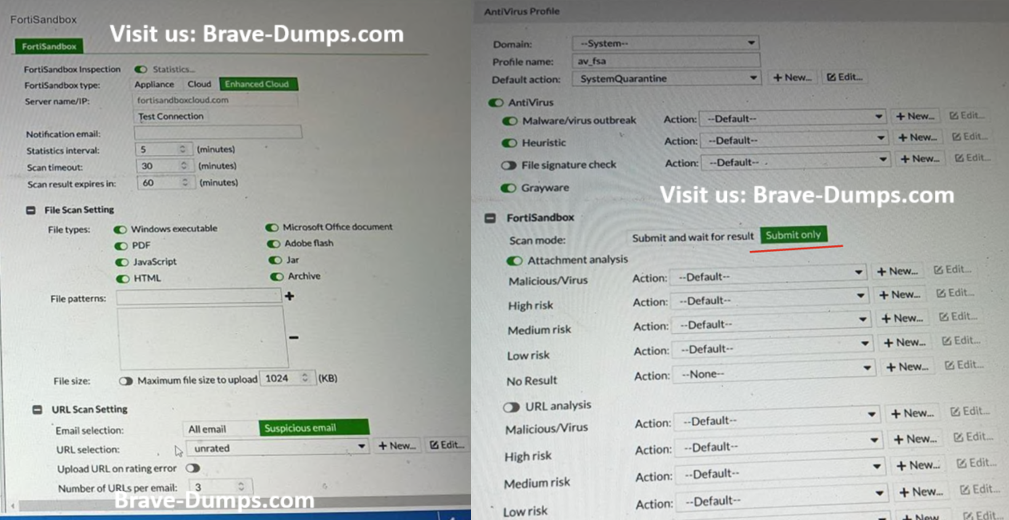
Refer to the exhibits.
You must integrate a FortiMail and FortiSandbox Enhanced Cloud solution for a customer who is concerned about the e-mails being delayed for too long.
According to the configuration shown in the exhibits, which would be an expected behavior?
(Choose one answer)
- A. FortiMail will ignore the timeout value if content disarm and reconstruction (CDR) is enabled.
- B. FortiMail will relay valid e-mails to the mail server as soon as it is done with other local inspections.
- C. If an attachment is sent to the FortiSandbox while the job queue is full, the e-mail might be delayed for up to 30 minutes, after that e-mail will be relayed to the mail server.
- D. FortiMail will not wait for results only for attachments that have been already submitted to the FortiSandbox in the last 60 minutes.
Question #5
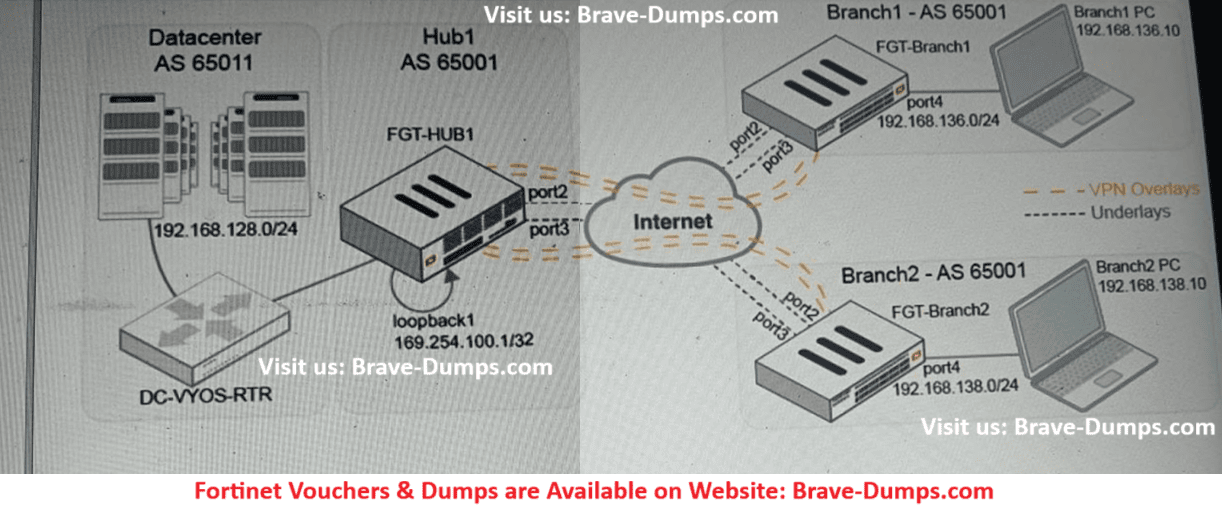
Refer to the exhibit, which shows a topology diagram.
A customer wants to use SD-WAN for traffic generated from the data center towards Branches. SD-WAN on HUB should follow the underlay condition on each Branch and the solution should be scalable for hundreds of Branches.
Which SD WAN-Rules strategy should be used?
(Choose one answer)
- A. Lowest Cost SLA
- B. Manual based on route-tags
- C. Best Quality based on route-tags
- D. Auto based on link quality
Question #6
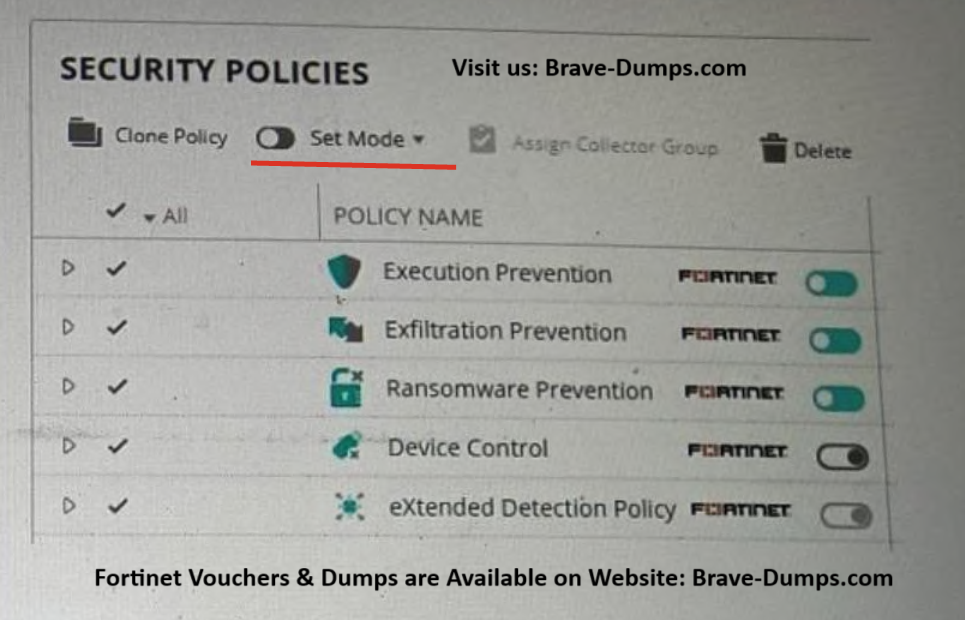
Refer to the exhibit showing a FortiEDR configuration.
Based on the exhibit, which statement is correct?
(Choose one answer)
- A. FortiEDR Collector will not collect OS Metadata.
- B. The presence of a cryptolocker malware at rest on the filesystem will be detected by the Ransomware Prevention security policy.
- C. If an unresolved file rule is triggered, by default the file is logged but not blocked.
- D. If a malicious file is executed and attempts to establish a connection it will generate duplicate events.
Question #7
A customer has FortiAP devices in three branch offices managed from a FortiGate in the HQ. Each FortiAP is connected to a dedicated management VLAN.
The customer wants the users connected to the FortiAP SSIDs to use the branch local internet connection, but each branch uses a different VLAN ID for the bridge. HQ users travel to different branches and connect to the same SSID.
Which configuration option will solve this requirement?
(Choose one answer)
- A. Set a FortiAuthenticator for 802.1x authentication with the Tunnel-Type attribute set to VLAN and use set dynamic-vlan enable on the VAP configuration.
- B. Use set vlan-pooling hash on the VAP configuration with the corresponding vlan-pool.
- C. Use set vlan-pooling round-robin on the VAP configuration with the corresponding vlan-pool.
- D. Set each FortiAP to a wtp-group and use set vlan-pooling wtp-group on the VAP configuration with the corresponding VLAN ID configuration for each group.
Question #8
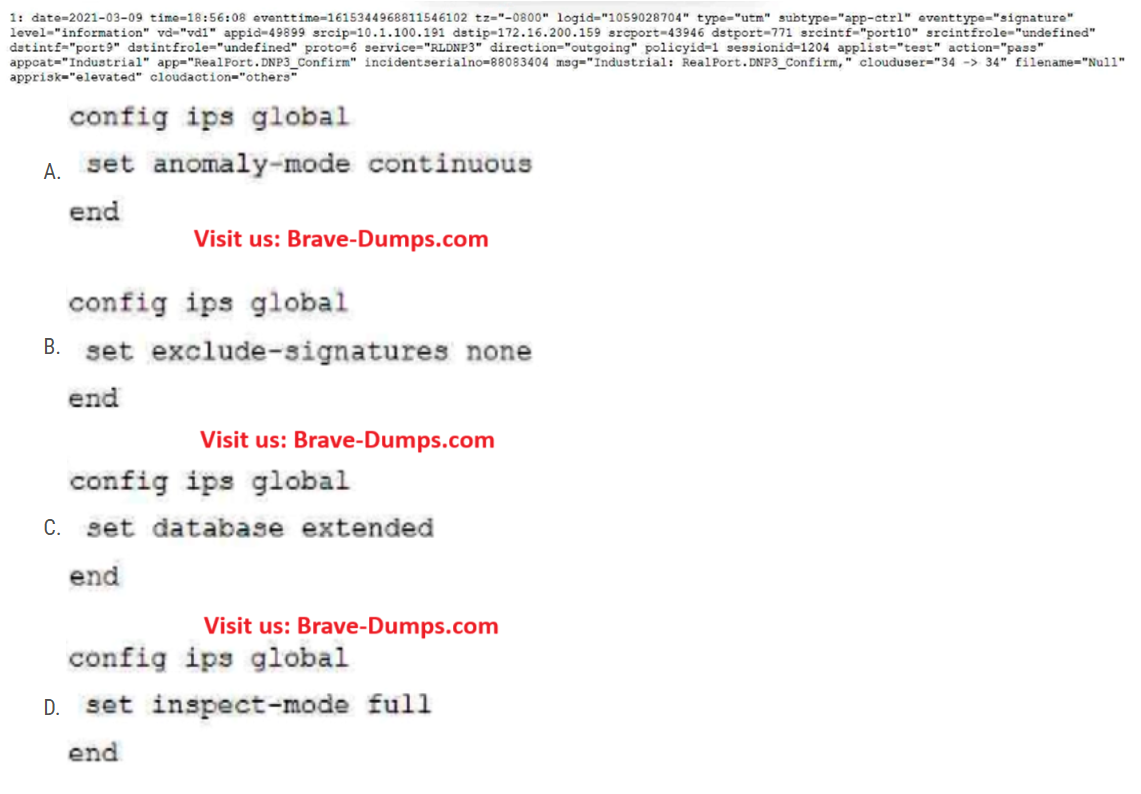
Review the Application Control log:
Which configuration caused the IPS engine to generate this log?
(Choose one answer)
- A. Image A
- B. Image B
- C. Image C
- D. Image D
Question #9
A FortiGate must be configured to accept VoIP traffic which will include session initiation protocol (SIP) traffic.
Which statement about the VoIP configuration options is correct?
(Choose one answer)
- A. By default, VoIP traffic will be processed using the SIP Session Helper.
- B. Restricting SIP requests is only possible when using the SIP Session Helper.
- C. FortiOS cannot accept SIP traffic if both the SIP Session Helper and the application layer gateway (ALG) are disabled.
- D. Rate tracking of SIP requests is only possible when the application layer gateway (ALG) is set to Flow mode.
Question #10
Which two statements about bounce address tagging and verification (BATV) on FortiMail are true? (Choose two answers)
- A. FortiMail will insert the BATV tag to the sender address in the envelope.
- B. Emails with an empty sender address will be subjected to bounce verification.
- C. You must publish the BATV public key as a DNS TXT record.
- D. BATV must be enabled in a session profile applied to an inbound IP policy.
You deployed a fully loaded FG-7121F in the data center and enabled sslvpn-load-balance.
Based on the behavior of this feature which statement is correct? (Choose one answer)