● NSE 6 - OT Security 7.2 Architect Exam Materials
Please note that the exam "NSE 6 - OT Security 7.2 Architect" is no longer offered by Fortinet and is not available for booking through Pearson VUE, so we opened it on free view,
It has been replaced by the exam "NSE 6 - OT Security 7.6 Architect"
The new exam version is available on Brave-Dumps and can be purchased.
It has been replaced by the exam "NSE 6 - OT Security 7.6 Architect"
The new exam version is available on Brave-Dumps and can be purchased.
Question #61
Question #62
FortiGate devices as well as FortiAnalyzer and FortiSIEM for the OT network.
Which two steps must you take to configure logging on the OT network?
(Choose two answers)
- A. Configure FortiGate and FortiAnalyzer to send industrial signature patterns to FortiSIEM.
- B. Configure FortiGate to send logs to FortiAnalyzer and FortiSIEM
- C. Configure FortiSIEM to send logs and alerts to FortiAnalyzer
- D. Configure FortiAnalyzer to send security events to FortiSIEM.
Question #63
An OT network consists of multiple FortiGate devices. The edge FortiGate device is deployed as the secure gateway and is only allowing remote operators to access the ICS networks on site.
Management hires a third-party company to conduct health and safety on site. The third-party company must have outbound access to external resources.
As the OT network administrator, what is the best scenario to provide external access to the third-party company while continuing to secure the ICS networks?
(Choose one answer)
- A. Split the edge FortiGate device into multiple logical devices to allocate an independent VDOM for the third-party company.
- B. Create VPN tunnels between downstream FortiGate devices and the edge FortiGate to protect ICS network traffic.
- C. Implement an additional firewall using an additional upstream link to the internet.
- D. Configure outbound security policies with limited active authentication users of the third-party company.
Question #64

Refer to the exhibit.
An operational technology rule is created and successfully activated to monitor the Modbus protocol on FortiSIEM. However, the rule does not trigger incidents despite Modbus traffic and application logs being received correctly by FortiSIEM.
Which statement correctly describes the issue on the rule configuration?
(Choose one answer)
- A. The attributes in the Group By section must match the ones in Filters section.
- B. The first condition on the SubPattern filter must use the OR logical operator.
- C. The SubPattern is missing the filter to match the Modbus protocol.
- D. The Aggregate attribute COUNT expression is incompatible with the filters.
Question #65
To increase security protection in an OT network, how does application control on FortiGate detect industrial traffic? (Choose one answer)
- A. By inspecting applications only on nonprotected traffic
- B. By inspecting applications with more granularity by inspecting subapplication traffic
- C. By inspecting protocols used in the application traffic
- D. By inspecting software and software-based vulnerabilities
Question #66
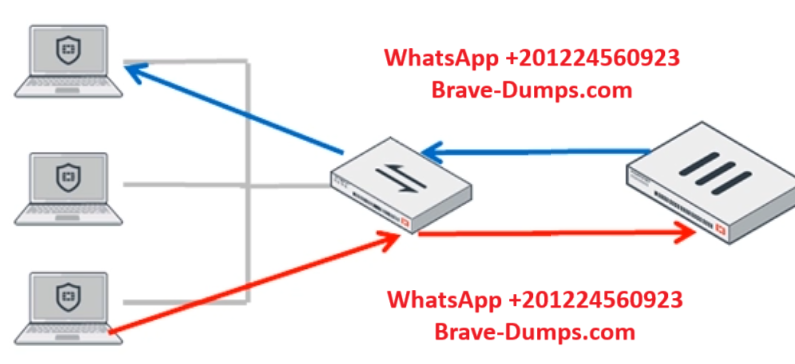
Refer to the exhibit.
An OT network architect must implement inter-VLAN routing in the topology. Traffic from each client is tagged with a unique VLAN. Each client is directly connected to a Layer 2 switch.
Which action must the OT network architect take to achieve this goal?
(Choose one answer)
- A. Configure a software switch to handle traffic for each client.
- B. Set the same forward domain on each switch interface.
- C. Replace the switch with a Layer 3 device.
- D. Make FortiGate a router on a stick.
Question #67
An organization has deployed an entry-level FortiGate device in their OT network. The administrator is looking for a simple solution to detect and block all network intrusions in that specific part of the network, without any false positive activities.
Which solution should the administrator use to achieve this goal?
(Choose one answer)
- A. Enable IPS and use the regular signature database.
- B. Enable IPS and use the protected signature database.
- C. Enable IPS and use the extreme signature database.
- D. Enable IPS and use the extended signature database.
Question #68
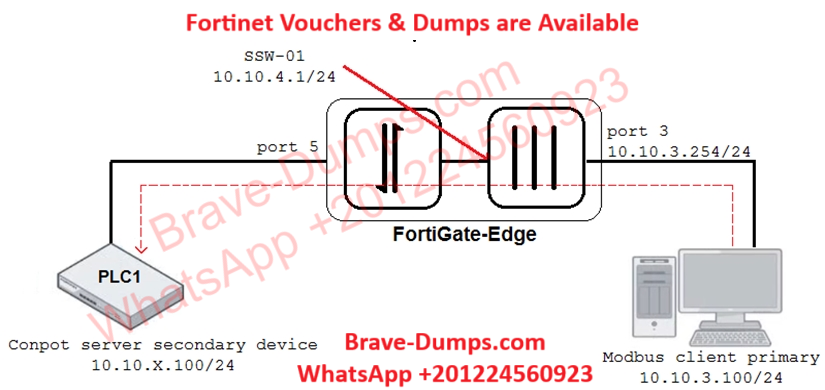
Refer to the exhibit.
An operational technology (OT) architect has implemented Modbus TCP with a simulation Conpot server to identify and control Modbus traffic in their OT network. The FortiGate-Edge device is configured with a software switch interface, SSW-01.
Based on the topology shown in the exhibit, which two statements must be true for the simulation of traffic between client and server to be successful?
(Choose two answers)
- A. An IP address must be assigned to port5.
- B. The FortiGate-Edge device must be in network address translation (NAT) operation mode.
- C. The FortiGate device must be in offline intrusion detection system (IDS) mode.
- D. In the FortiGate firewall policy, NAT must be enabled from port3 to SSW-01.
Question #69
What is the primary objective of implementing SD-WAN in operational technology (OT) networks? (Choose one answer)
- A. Enhance network performance of OT applications.
- B. Reduce security risk and threat attacks.
- C. Remove centralized network security policies.
- D. Replace standard links with lower cost connections.
Question #70
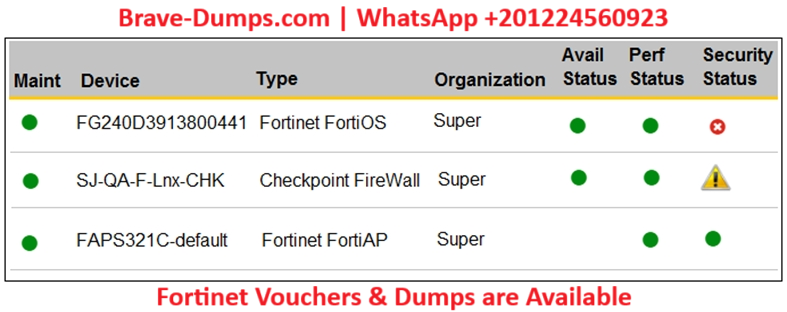
Refer to the exhibit.
You are navigating through FortiSIEM in an OT network.
How do you view information presented in the exhibit and what does the FortiGate device security status tell you?
(Choose one answer)
- A. In the PCI logging dashboard and there are one or more high-severity security incidents for the FortiGate device.
- B. In the summary dashboard and there are one or more high-severity security incidents for the FortiGate device.
- C. In the widget dashboard and there are one or more high-severity incidents for the FortiGate device.
- D. In the business service dashboard and there are one or more high-severity security incidents for the FortiGate device.
An OT network architect needs to secure control area zones with a single network access policy to provision devices to any number of different networks.
On which device can this be accomplished? (Choose one answer)